Say “dead puppy in the over head bin” or “comfort peacock” and I’m guessing most folks will know what you’re talking about. A Google search finds nearly two million references to the event last month in which a dog suffocated after a flight attendant ordered its owners to put the crated puppy in the overhead bin.
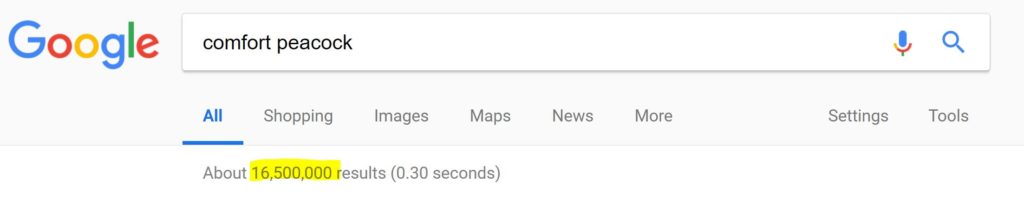
A stunning 16 million references litter the Google landscape related to the passenger who tried to board a United flight with a comfort peacock in tow.
Without diminishing the trauma of the family of the pup, “Coquito” or the curiosity factor related to anyone choosing to fly with a peacock, let’s compare these with the far more consequential event last week, when aircraft manufacturer Boeing became the latest victim of the WannaCry virus.
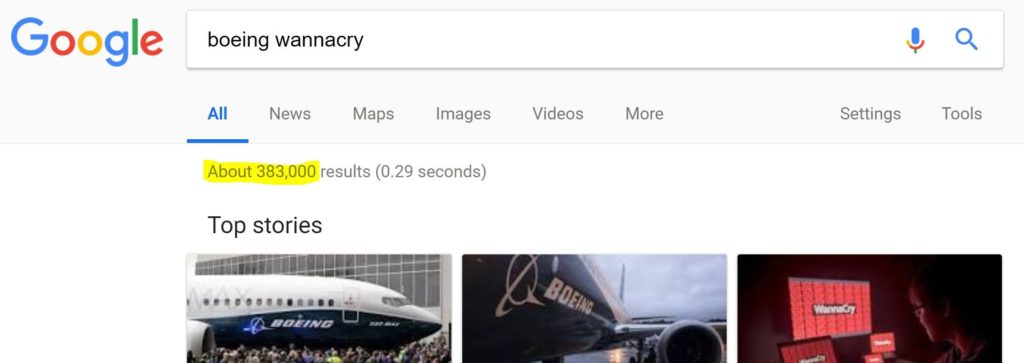
According to a memo obtained by Dominic Gates of the Seattle Times from the chief engineer at Boeing Commercial Airplane production engineering, the company’s South Carolina Dreamliner assembly plant was attacked by the malware virus WannaCry, an event the memo’s writer Mike VanderWel claimed was “metastasizing rapidly out of North Charleston”. VanderWel worried that the assembly tools on the Boeing 777 might have also been affected and called for “all hands on deck.”

Boeing quickly disputed the media accounts with a statement saying, “Our cyber security operations center detected a limited intrusion of malware that affected a small number of systems.” And that seems to be that, at least as far general media reports go. We’ve seen this “yes its a problem/no its not a problem” before.
Last Spring, Robert Hickey, a cyber security expert specializing in aviation for the Department of Homeland Security, surprised an audience when he reported his team purchased and tested a Boeing 757 at the Federal Aviation Administration’s technical center in Atlantic City, New Jersey.
“We got the airplane on Sept. 19, 2016. Two days later, I was successful in accomplishing a remote, non-cooperative, penetration,” he told the CyberSat Summit in Virginia. Using radio frequency communication, “I stood off using typical stuff that could get through security and we were able to establish a presence on the systems of the aircraft.”
Hickey’s report is classified he said, and there’s no independent analysis of it that I can find. A security expert for the International Air Transport Association told me in December that Hickey’s findings had not been substantiated, but there’s no public report on that either.
Others in the industry are concerned, including Joel Otto, vice president at Information Management Services, part of Rockwell Collins. “There are a variety of potential vulnerabilities,” Otto told me at a press briefing in Virginia. This was Wednesday morning, before the news broke about Boeing’s Dreamliner plant being hit. The challenge, Otto explained, is “how to design the aircraft against threats on and off.”
“Cyber threats are ever-moving with ever-changing targets,” he told me.
As a aviation writer specializing in safety, security is outside of my field of expertise. Still, the two subjects are on a collision course as aircraft operating systems grow increasingly reliant on manufacturer software. That’s why it is so important for journalists to pursue stories about aviation cyber threats with the same energy they apply to stories about dead dogs and companion peacocks. That’s not happening with the WannaCry hack of Boeing, though there’s little doubt its a story that could end tears.

First 787 Takeoff In Charleston SC
K65673

Author of The New York Times bestseller, The Crash Detectives, I am also a journalist, public speaker and broadcaster specializing in aviation and travel.